Your search did not yield any results.
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- Fast Track to Java 17 and OO Development
12 August, 2024 - 16 August, 2024 - RED HAT ENTERPRISE LINUX AUTOMATION WITH ANSIBLE
29 July, 2024 - 1 August, 2024 - Introduction to C++ for Absolute Beginners
14 October, 2024 - 15 October, 2024 - DOCKER WITH KUBERNETES ADMINISTRATION
8 July, 2024 - 12 July, 2024 - RHCSA EXAM PREP
9 September, 2024 - 13 September, 2024 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
As much as we love to assume free Wi-Fi is secure, this is far from the truth. Because you are attaching to a service many others are connected to as well, without security measures, your device can be hacked, especially if the network is unencrypted. Because this encryption involves handing out a 26-character hexadecimal key to every individual wanting to use that network, most places opt for ease of access over security. And even with a secure network, your information is vulnerable to everyone else who has the password and is on the network.
This may not seem like such a big deal and many people don’t believe they have anything to hide on their personal devices, but remember what you use on those devices. Chances are your e-mail is attached as well as all other social media sites. You may have apps that track your finances or private messages to certain others that you would never want anyone else to see. Luckily, there are steps that can be taken to reduce and prevent any unwanted information grabbers from accessing your personal information.
To start, go through your computer’s settings in order to verify your operating system’s security functions are all set to offer the highest protection. Open up the Control Panel and double check that your Firewall is enabled for both private and public networks. Then, go to Network and Sharing to open Change advanced sharing settings. In here, you can turn off file and printer sharing and network discovery for public networks.
One of the most important things to watch for is HTTPS. Hypertext Transfer Protocol Secure ensures secure communication across the web. Many of the major email systems use this when you log in (as another layer of password protection) but drop the security as soon as the login is complete. To keep this going, HTTPS Everywhere is a browser extension that gives you a secure connection when browsing some of the more popular sites. It can also be programmed for other sites you like to visit that don’t use HTTPS.
Not every place on the internet provides the choice of HTTPS, and VPNs are there to fill in the security gap. Virtual Private Networks allows data to be sent and received through public access points as if it were directly connected to a secure network. Many businesses offer this for company devices, but if you are an individual looking for that kind of security, ProXPN is a free version that can be upgraded. Unfortunately, it limits your speed, but other choices include VPNBook, OpenVPN Shield Exchange, and OkayFreedom.
With these three steps implemented, secure public Wi-Fi can be achieved. No longer will you have to worry about connecting in an unsure environment with strangers, never knowing if your information is being stolen. With all of the options free of charge, it is also an affordable means of protecting yourself that only takes a little time and effort to implement and guarantee safety.
Net Neutrality for the Layperson
What are a few unique pieces of career advice that nobody ever mentions?
The world of technology moves faster than the speed of light it seems. Devices are updated and software upgraded annually and sometimes more frequent than that. Society wants to be able to function and be as productive as they can be as well as be entertained “now”.
Software companies must be ready to meet the demands of their loyal customers while increasing their market share among new customers. These companies are always looking to the ingenuity and creativity of their colleagues to keep them in the consumer’s focus. But, who are these “colleagues”? Are they required to be young, twenty-somethings that are fresh out of college with a host of ideas and energy about software and hardware that the consumer may enjoy? Or can they be more mature with a little more experience in the working world and may know a bit more about the consumer’s needs and some knowledge of today’s devices?
Older candidates for IT positions face many challenges when competing with their younger counterparts. The primary challenge that most will face is the ability to prove their knowledge of current hardware and the development and application of software used by consumers. Candidates will have to prove that although they may be older, their knowledge and experience is very current. They will have to make more of an effort to show that they are on pace with the younger candidates.
Another challenge will be marketing what should be considered prized assets; maturity and work experience. More mature candidates bring along a history of work experience and a level of maturity that can be utilized as a resource for most companies. They are more experienced with time management, organization and communication skills as well as balancing home and work. They can quickly become role models for younger colleagues within the company.
Unfortunately, some mature candidates can be seen as a threat to existing leadership, especially if that leadership is younger. Younger members of a leadership team may be concerned that the older candidate may be able to move them out of their position. If the candidate has a considerably robust technological background this will be a special concern and could cause the candidate to lose the opportunity.
Demonstrating that their knowledge or training is current, marketing their experience and maturity, and not being seen as a threat to existing leadership make job hunting an even more daunting task for the mature candidate. There are often times that they are overlooked for positions for these very reasons. But, software companies who know what they need and how to utilize talent will not pass up the opportunity to hire these jewels.
Related:
H-1B Visas, the Dance Between Large Corporations and the Local IT Professional
Is a period of free consulting an effective way to acquire new business with a potential client?
Facebook was originally intended as a way for people to stay in touch with friends and family members by sharing pictures and status updates on their timeline. As the website's popularity has grown, so has criticism that it is becoming one giant, online high school.
Online Bullying
 There has been a dramatic increase in recent years in the number of online bullying cases due to the introduction of social media. Bullying isn't just limited to younger Facebook users, either. Many adult users have also resorted to bashing others online through nasty status updates and cruel comments.
There has been a dramatic increase in recent years in the number of online bullying cases due to the introduction of social media. Bullying isn't just limited to younger Facebook users, either. Many adult users have also resorted to bashing others online through nasty status updates and cruel comments.
Prior to social media, bullying in high school involved "kick me" signs and toilet swirling. Facebook and other social media outlets have allowed users to take bullying to a whole other level. Victims can no longer escape bullying by leaving school or work. The torture continues online, at anytime and anyplace.
Status "Likes"
In high school, everyone wants to be part of the popular crowd; people who are outgoing, beautiful, and seem like they have everything. Posting a status update is similar to wanting to be popular. Once an update is posted, many users wait with bated breath to see how many friends will "like" their status. They believe that the more "likes" they receive, the more popular they are.
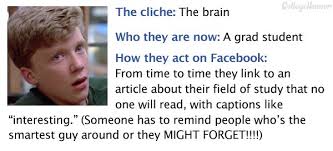 If that isn’t enough, there are many Facebook games that involve "liking" someone's status. Games like "Truth Is", where someone likes a status update and in return the poster writes how they really feel about the friend on their Facebook wall. This can get touchy, especially if the two people aren't friends outside of Facebook. It's similar to high school where someone desperately wants another person to like them, but when they find out how that person really feels they are crushed.
If that isn’t enough, there are many Facebook games that involve "liking" someone's status. Games like "Truth Is", where someone likes a status update and in return the poster writes how they really feel about the friend on their Facebook wall. This can get touchy, especially if the two people aren't friends outside of Facebook. It's similar to high school where someone desperately wants another person to like them, but when they find out how that person really feels they are crushed.
Relationships Are Difficult to Keep Private
When someone signs up for Facebook they’re asked to complete their profile, which includes a relationship section. Users can select from different options including "single", "married", "widowed", and "divorced". Whenever someone changes their relationship status, the update shows up on each of their friend's news feeds.
It's easy to see how this feature correlates with high school where everyone talks about who is dating who or which couple broke up. It used to be that after graduation, people were able to keep their relationships more to themselves. Not so anymore in the age of social media. Now everyone has the ability to state their opinion on a friend's relationship status, either by "liking" their status change or by commenting on it.
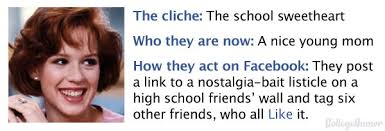 Facebook has presented many benefits to its users, including the ability to rekindle old high school friendships. What one must understand when they sign up for the service is that they are opening themselves up to the same criticism and drama that takes place in a high school setting.
Facebook has presented many benefits to its users, including the ability to rekindle old high school friendships. What one must understand when they sign up for the service is that they are opening themselves up to the same criticism and drama that takes place in a high school setting.
Proceed with caution!
We’re often asked by companies about how they can get the most value from Agile/Scrum practices. More specifically, they want to know if they are being as effective as best they possibly can be by using the Scrum framework for their explicit needs.
The other objective for individuals is determining if it necessary to be certified in order to be effective in the Agile Scrum world? In short, a good Scrum Master must understand four things: the business they work in, the technology they work with, the Agile and Scrum principles, and, most importantly, people! Based on these facts, Scrum Master Certification is not enough – real life experience and a bit of soft skills should be part and parcel of their training. For organizations, the main goal is to understand industry best practices when adopting and applying agile principles, to build strong teams, understand and distill business needs into software requirements.
In terms of getting a good grip on training for Agile/Scrum, one can opt to pursue a certification in Scrum (CSM) Certified Scrum Master for personal reasons or for a job requirement. Or, one can simply opt to learn the benefits and pitfalls of the methodology and decide the best approach for them.
There are different ways to get started with Agile training. Below are two of the most common paths to Agile our students take.
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about programming
- Get your questions answered by easy to follow, organized experts
- Get up to speed with vital programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…