Git, Jira, Wicket, Gradle, Tableau Training Classes in Wilmington, Delaware
Learn Git, Jira, Wicket, Gradle, Tableau in Wilmington, Delaware and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Git, Jira, Wicket, Gradle, Tableau related training offerings in Wilmington, Delaware: Git, Jira, Wicket, Gradle, Tableau Training
Git, Jira, Wicket, Gradle, Tableau Training Catalog
subcategories
Agile/Scrum Classes
Git Classes
Gradle Classes
Jira/Cofluence Classes
Tableau Classes
Wicket Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- Object-Oriented Programming in C# Rev. 6.1
24 June, 2024 - 28 June, 2024 - RED HAT ENTERPRISE LINUX AUTOMATION WITH ANSIBLE
3 June, 2024 - 6 June, 2024 - ASP.NET Core MVC, Rev. 6.0
19 August, 2024 - 20 August, 2024 - Introduction to C++ for Absolute Beginners
20 May, 2024 - 21 May, 2024 - OpenShift Fundamentals
24 June, 2024 - 26 June, 2024 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
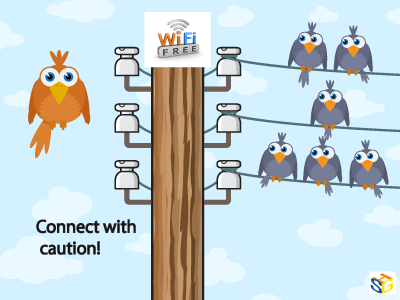
As much as we love to assume free Wi-Fi is secure, this is far from the truth. Because you are attaching to a service many others are connected to as well, without security measures, your device can be hacked, especially if the network is unencrypted. Because this encryption involves handing out a 26-character hexadecimal key to every individual wanting to use that network, most places opt for ease of access over security. And even with a secure network, your information is vulnerable to everyone else who has the password and is on the network.
This may not seem like such a big deal and many people don’t believe they have anything to hide on their personal devices, but remember what you use on those devices. Chances are your e-mail is attached as well as all other social media sites. You may have apps that track your finances or private messages to certain others that you would never want anyone else to see. Luckily, there are steps that can be taken to reduce and prevent any unwanted information grabbers from accessing your personal information.
To start, go through your computer’s settings in order to verify your operating system’s security functions are all set to offer the highest protection. Open up the Control Panel and double check that your Firewall is enabled for both private and public networks. Then, go to Network and Sharing to open Change advanced sharing settings. In here, you can turn off file and printer sharing and network discovery for public networks.
One of the most important things to watch for is HTTPS. Hypertext Transfer Protocol Secure ensures secure communication across the web. Many of the major email systems use this when you log in (as another layer of password protection) but drop the security as soon as the login is complete. To keep this going, HTTPS Everywhere is a browser extension that gives you a secure connection when browsing some of the more popular sites. It can also be programmed for other sites you like to visit that don’t use HTTPS.
Not every place on the internet provides the choice of HTTPS, and VPNs are there to fill in the security gap. Virtual Private Networks allows data to be sent and received through public access points as if it were directly connected to a secure network. Many businesses offer this for company devices, but if you are an individual looking for that kind of security, ProXPN is a free version that can be upgraded. Unfortunately, it limits your speed, but other choices include VPNBook, OpenVPN Shield Exchange, and OkayFreedom.
With these three steps implemented, secure public Wi-Fi can be achieved. No longer will you have to worry about connecting in an unsure environment with strangers, never knowing if your information is being stolen. With all of the options free of charge, it is also an affordable means of protecting yourself that only takes a little time and effort to implement and guarantee safety.
Net Neutrality for the Layperson
What are a few unique pieces of career advice that nobody ever mentions?
The iconic software company that is based in King County Washington has been getting almost universally slammed from it's recent Los Angeles press announcement about its entry into the hardware business with the convertible laptop/tablet known as Surface.
Certainly I can see the point that it is now competing with its hardware vendors/partners. Intel has done a good job in the arena creating 'reference designs' without competing with its partners.
There is another viewpoint which seems to be ignored. The cold facts are Microsoft is a public company. This puts Microsoft in a legal position of doing the most it can to return value to its shareholders. Failure to do so means somebody is going to jail.
Microsoft has a vision, which at the end of the day is, a certain way to get enough people to see enough value to hand over their money, to fulfill their fiduciary duty.
This section of our beginning python training class always stumps students. Firstly, because they need to know the difference between a function and a method. Secondly, they need to understand object oriented programming concepts. Thirdly, they need to realize that python has three types of methods. Then they need to know how to use each method, which means they need to know the purpose of each method type. Then they have to understand mutable versus non-mutable types. The list goes on. As part of our python tutorial, I hope to shed some light on this confusing topic.
To begin, the difference between a function and a method in python is that a method is defined within a class. Here is an illustration:
#function def greeting(): print "Hello, I hope you're having a great day!" class HSGPrinter(object): #method def greeting(self): print "Hello, I hope you're having a great day!"
As should be obvious, the second definition of greeting is encapsulated within the HSGPrinter class and is , therefore, refered to as a method.
The astute reader will notice that the greeting method contains one parameter named self. For those who know C++ , Java or C#, self is equivalent to this i.e. it is a reference to the invoking object:
Like me, I believe most people go about their business never to give a serious thought about their assumed private correspondence when using Gmail to email friends, colleagues and business associates. As it turns out, your daily banter may not be so private after all. A recent article in Fortune Magazine, “Judge Rejects Google Deal Over Email Scanning” caught my attention and an immediate thought dominated my curiosity…Google email and scanning scam.
In essence, the article describes Googles’ agreement to change the way it scans incoming messages so that it no longer reads emails while they are in transit, but only when they are in someone's inbox! So, what exactly does that mean? Judge Koh, a San Francisco federal judge, said she's not so sure about that. Her ruling claims the settlement does not provide an adequate technical explanation of Google's workaround, which involves scanning in-transit emails for security purposes, and then later parsing them for advertising data. The judge also proposed a legal settlement to pay $2.2 million to lawyers, but nothing to consumers.
My interest in this story is not so much about the proposed settlements or the specific details about how Google or any of the web giants settle claims based on vague legal language. It is however, more about the naiveté of myself and perhaps many others that never question how the email scanning process really works. I wonder, do most of us really care that Gmail uses contents of our mail to display targeted ads?
Tech Life in Delaware
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Delphi Financial Group, Inc. | Wilmington | Financial Services | Insurance and Risk Management |
| DuPont | Wilmington | Manufacturing | Manufacturing Other |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Delaware since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Git, Jira, Wicket, Gradle, Tableau programming
- Get your questions answered by easy to follow, organized Git, Jira, Wicket, Gradle, Tableau experts
- Get up to speed with vital Git, Jira, Wicket, Gradle, Tableau programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…

![Computer Graphics Programming in OpenGL with C++ [With CD (Audio)]](/bookim/9781683922216.jpg)