JBoss Administration Training Classes in Shoreline, Washington
Learn JBoss Administration in Shoreline, Washington and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current JBoss Administration related training offerings in Shoreline, Washington: JBoss Administration Training
JBoss Administration Training Catalog
JBoss Administration Classes
Java Enterprise Edition Classes
Java Programming Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- RED HAT ENTERPRISE LINUX V7 DIFFERENCES
13 May, 2024 - 15 May, 2024 - Introduction to Python 3.x
22 July, 2024 - 25 July, 2024 - VMware vSphere 8.0 with ESXi and vCenter
10 June, 2024 - 14 June, 2024 - Linux Fundaments GL120
15 July, 2024 - 19 July, 2024 - RED HAT ENTERPRISE LINUX AUTOMATION WITH ANSIBLE
3 June, 2024 - 6 June, 2024 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
One of the most recent additions to the iPhone is the Photo Editor, directly in the iPhone. Added in the update that came from Apple over the summer, this new photo editor brings efficiency, and simplicity to photo editing, right in your phone. If you have a photo that you just took a moment ago of you with your friends, and you want to edit some features before posting it on a social networking site, it becomes simpler with this new addition, right in the Photos Application.
Open up the Photos application, and tap on a picture you would like to edit. Once your picture comes up, tap in the top right on the button named “Edit.” A user interface that deals with editing will show up, and you are ready to rock and roll. First off, many times we take pictures at weird angles, we take them sideways, upside down, to the right, to the left, and our phone doesn’t recognize them. In the bottom left, you will see an arrow that is pointing counter clockwise; this is the button that you want to press if you want to flip your picture around to the correct orientation. Keep in mind that this flips counter clockwise, and it doesn’t matter if you pass the orientation that you wanted. Just keep flipping!
Next up is the simple enhance tool. Sometimes colors get drowned out if we don’t have the right lighting in our pictures, and makes the photo look dull, and dreary. You don’t want your colors to look dull and dreary while you are celebrating your trip to New York and seeing Times Square! Tapping on the button that looks similar to a magic wand, your picture will begin to look brighter and fuller. With the tap of a button, the iPhone detects what points in the picture is, as we said earlier, “dull, and dreary” and enhances those colors to their predicted colors, if the light was in the correct intensity. However, if you are dissatisfied with the outcome of the enhance tool, if your picture is not handled well by the phone, you are able to tap on the wand again, and remove your auto enhance.
In the rare case of red eye in your picture, the new photo editor has a solution. Moreover, a one-tap solution. With a simple tap on the red eye correction tool, between the crop tool, and the auto-enhance tool, you bring up a screen where you are now able to tap anywhere on your photo where red eye exists, and remove it. As simple as that. Remember when you had to do crazy dragging, selection, and odd stunts to remove red eye? Not any more.
I will begin our blog on Java Tutorial with an incredibly important aspect of java development: memory management. The importance of this topic should not be minimized as an application's performance and footprint size are at stake.
From the outset, the Java Virtual Machine (JVM) manages memory via a mechanism known as Garbage Collection (GC). The Garbage collector
- Manages the heap memory. All obects are stored on the heap; therefore, all objects are managed. The keyword, new, allocates the requisite memory to instantiate an object and places the newly allocated memory on the heap. This object is marked as live until it is no longer being reference.
- Deallocates or reclaims those objects that are no longer being referened.
- Traditionally, employs a Mark and Sweep algorithm. In the mark phase, the collector identifies which objects are still alive. The sweep phase identifies objects that are no longer alive.
- Deallocates the memory of objects that are not marked as live.
- Is automatically run by the JVM and not explicitely called by the Java developer. Unlike languages such as C++, the Java developer has no explict control over memory management.
- Does not manage the stack. Local primitive types and local object references are not managed by the GC.
So if the Java developer has no control over memory management, why even worry about the GC? It turns out that memory management is an integral part of an application's performance, all things being equal. The more memory that is required for the application to run, the greater the likelihood that computational efficiency suffers. To that end, the developer has to take into account the amount of memory being allocated when writing code. This translates into the amount of heap memory being consumed.
Memory is split into two types: stack and heap. Stack memory is memory set aside for a thread of execution e.g. a function. When a function is called, a block of memory is reserved for those variables local to the function, provided that they are either a type of Java primitive or an object reference. Upon runtime completion of the function call, the reserved memory block is now available for the next thread of execution. Heap memory, on the otherhand, is dynamically allocated. That is, there is no set pattern for allocating or deallocating this memory. Therefore, keeping track or managing this type of memory is a complicated process. In Java, such memory is allocated when instantiating an object:
String s = new String(); // new operator being employed String m = "A String"; /* object instantiated by the JVM and then being set to a value. The JVM calls the new operator */
Information Technology is one of the most dynamic industries with new technologies surfacing frequently. In such a scenario, it can get intimidating for information technology professionals at all levels to keep abreast of the latest technology innovations worth investing time and resources into.
It can therefore get daunting for entry and mid-level IT professionals to decide which technologies they should potentially be developing skills. However, the biggest challenge comes for senior information technology professionals responsible for driving the IT strategy in their organizations.
It is therefore important to keep abreast of the latest technology trends and get them from reputable sources. Here are some of the ways to keep on top of the latest trends in Information Technology.
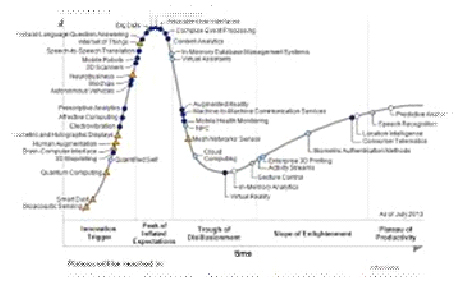
· Subscribe to leading Analyst Firms: If you work for a leading IT organization, chances are that you already have subscription to leading IT analyst firms notably Gartner and Forrester. These two firms are some of the most recognized analyst firms with extensive coverage on almost every enterprise technology including hardware and software. These Analyst firms frequently publish reports on global IT spending and trends that are based on primary research conducted on vendors and global CIOs & CTOs. However, subscription to these reports is very expensive and if you are a part of a small organization you may have issues securing access to these reports. One of the most important pieces of research published by these firms happens to be the Gartner Hype Cycle which plots leading technologies and their maturity curve.Even if you do not have access to Gartner research, you can hack your way by searching for “Gartner Hype Cycle” on Google Images and you will in most cases be able to see the plots similar to the one below
Tech Life in Washington
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Symetra Financial Corporation | Bellevue | Financial Services | Insurance and Risk Management |
| Alaska Air Group, Inc. | Seattle | Travel, Recreation and Leisure | Passenger Airlines |
| Expedia, Inc. | Bellevue | Travel, Recreation and Leisure | Travel Agents & Services |
| Itron, Inc. | Liberty Lake | Computers and Electronics | Instruments and Controls |
| PACCAR Inc. | Bellevue | Manufacturing | Automobiles, Boats and Motor Vehicles |
| Puget Sound Energy Inc | Bellevue | Energy and Utilities | Gas and Electric Utilities |
| Expeditors International of Washington, Inc. | Seattle | Transportation and Storage | Freight Hauling (Rail and Truck) |
| Costco Wholesale Corporation | Issaquah | Retail | Grocery and Specialty Food Stores |
| Starbucks Corporation | Seattle | Retail | Restaurants and Bars |
| Nordstrom, Inc. | Seattle | Retail | Department Stores |
| Weyerhaeuser Company | Federal Way | Manufacturing | Paper and Paper Products |
| Microsoft Corporation | Redmond | Software and Internet | Software |
| Amazon.com, Inc. | Seattle | Retail | Sporting Goods, Hobby, Book, and Music Stores |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Washington since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about JBoss Administration programming
- Get your questions answered by easy to follow, organized JBoss Administration experts
- Get up to speed with vital JBoss Administration programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…